Breach Prevention for Microsoft 365
Cybercriminals are increasingly bypassing traditional endpoints and networks and are instead targeting cloud identities to infiltrate organizations. Once access to an account is gained, they often roam freely, going undetected. Understanding when a user is performing actions that deviates from their typical routine is critical to stopping threats early.
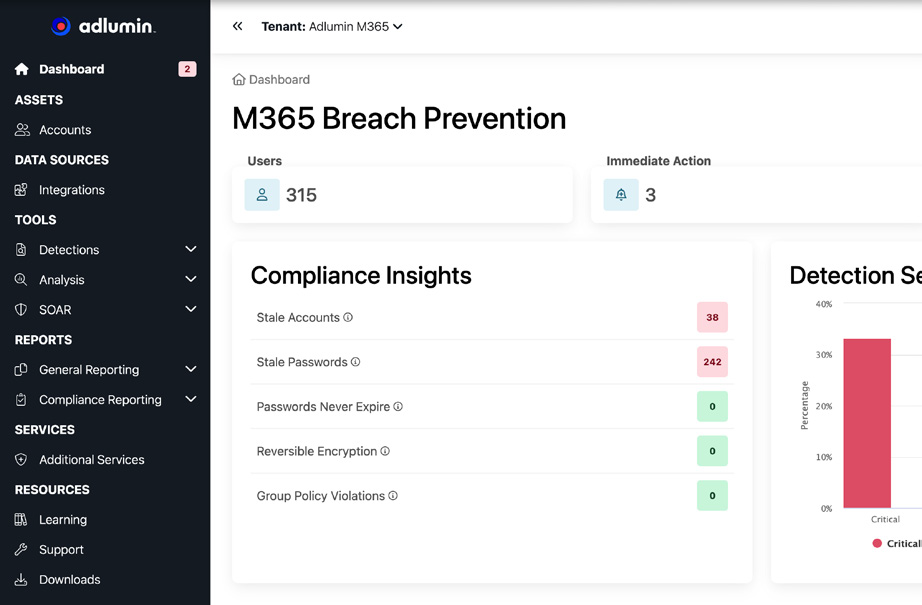
Advanced Threat Detection
Identity Protection
Real-Time Monitoring
User Account Security
How We Detect and Stop Threats

Proactive Threat Detection
Utilize cutting-edge technology to identify and neutralize threats before they compromise your system.

Dynamic Response
Intelligent response analyzes data and behavior analytics to assess the risk level and adjust action accordingly.

Automated Threat Mitigation
When suspicious activity is detected, the account in question either forces a password reset or is disabled.

Email-Based Attacks
Catches stealthy tactics like email forwarding rules and inbox manipulations designed to exfiltrate sensitive data.
How Our Software Protects Your Business
Step 1
Our software continuously scans for suspicious activities, identifying potential threats in real-time.
Step 2
Once a threat is detected, immediate actions are taken to isolate and neutralize the risk.
Step 3
Comprehensive reports provide insights and recommendations to strengthen your security posture.
Proven Results
Our breach prevention solutions have been shown to reduce identity attacks by 85% within the first year of implementation.
85% Reduction in Identity Attacks
Secure Your Business Today
Don’t leave your business vulnerable. Contact us to learn how our security solutions can protect your Microsoft 365 environment.
